What Are the 5 Rules of Staying Safe Online?
The internet, a vast and ever-expanding digital frontier, offers a treasure trove of information, connection, and endless entertainment. Norton’s research said that children are particularly vulnerable online due to their limited understanding of internet dangers. Teaching them to recognize and avoid suspicious activities is crucial for their safety. However, just like venturing into uncharted territory, navigating the online world requires a compass – a set of guidelines to ensure a safe and enriching experience.
This article delves beyond the basic “don’t share your password” advice. We’ll explore five crucial rules for online safety, equipping you with the knowledge to not only protect yourself but also empower you to participate confidently in the digital world.
Rule #1: Fort Knox Your Passwords – The Gatekeepers of Your Digital Identity
Imagine your online accounts as individual fortresses, each safeguarding sensitive information. Strong, unique passwords act as the formidable gatekeepers, deterring unauthorized access. Here’s how to craft impenetrable passwords:
- Length is Strength: Move beyond the standard 8 characters. Aim for 12 characters or more, incorporating a mix of uppercase and lowercase letters, numbers, and symbols.
- Uniqueness is Key: Resist the urge to reuse passwords across different platforms. A data breach on one site could compromise all your accounts if they share the same password.
- Outsmart the Hackers: Ditch easily guessable passwords like birthdays or pet names. Consider using a password manager – a secure application that stores and generates complex passwords for all your accounts.
Rule #2: Think Before You Click – Unveiling the Deceptive World of Phishing
Phishing scams are akin to online booby traps, disguised as legitimate emails or websites. They aim to trick you into revealing personal details like passwords or credit card information. Here’s how to identify and avoid these deceptive tactics:
- Suspicious Sender? Be wary of emails from unknown senders or those with misspelled domain names. Legitimate companies won’t pressure you into clicking on urgent links.
- Scrutinize the Link: If you hover over a link in an email, your browser should display the actual destination URL. Don’t click on links that appear suspicious or lead to unexpected websites.
- Guarded Attachments: Emails with unexpected attachments, especially from unknown senders, can harbor malware. Refrain from opening them unless you’re absolutely certain of their origin.
Also Read: How do ultrasonic cleaning machines work?
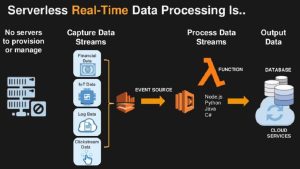
Rule #3: Building a Digital Fortress – Securing Your Devices and Networks
Just as a physical fortress needs strong walls, your digital devices require robust security measures. Here’s how to fortify your defenses:
- Software Updates: Those pesky update notifications aren’t just nagging reminders. They often contain crucial security patches that address vulnerabilities exploited by hackers. Make it a habit to update your operating system, web browser, and applications regularly.
- Antivirus Armor: Think of an antivirus program as a digital suit of armor, constantly scanning for and neutralizing malicious software (malware) like viruses and spyware. Choose a reputable antivirus solution and keep it updated for optimal protection.
- The Power of Encryption: Public Wi-Fi networks, while convenient, are often unsecured. When accessing sensitive information on public Wi-Fi, consider using a Virtual Private Network (VPN). A VPN encrypts your internet traffic, making it unreadable to prying eyes.
Rule #4: Guarding Your Digital Reputation – What You Share Shapes Your Online Persona
The internet has a long memory. Information you share online, whether a witty comment or a vacation photo, can leave a lasting digital footprint. Here’s how to curate a positive online presence:
- Think Twice Before You Post: Consider the potential consequences of your online activity. Would you share that information with someone you just met? If not, it’s probably best to refrain from posting it online.
- Privacy Settings Matter: Most social media platforms allow you to control who sees your posts. Review and adjust your privacy settings to ensure only intended audiences have access to your information.
- Beware of Oversharing: While social media connects us, it’s important to maintain boundaries. Avoid sharing overly personal details like your home address or phone number on public platforms.
Rule #5: Navigating the Social Jungle – Cultivating Healthy and Safe Online Interactions
The internet facilitates connection and community building. However, it’s essential to be mindful of your online interactions. Here’s how to foster safe and positive online relationships:
- Stranger Danger Applies Online Too: Just like in the real world, be cautious when interacting with strangers online. Never share personal information with people you don’t know and trust.
- The Power of “Report” and “Block”: Don’t hesitate to report abusive or harassing behavior on social media platforms. Most platforms have reporting mechanisms in place to handle misconduct. Additionally, utilize the “block” function liberally to prevent unwanted interactions.
- The Dangers of Cyberbullying: Sadly, online bullying is prevalent. If you or someone you know is experiencing cyberbullying, don’t suffer in silence. Seek help from a trusted adult, report the behavior to the platform, and consider documenting the incidents.
Staying Informed, Staying Vigilant
Remember, online safety is an ongoing process. The digital landscape evolves, and so do the tactics used by cybercriminals. These additional tips will help you stay ahead of the curve:
- News is Your Arsenal: Stay updated on the latest scams and security threats by subscribing to online security blogs or newsletters. Knowledge is your best defense.
- If It Seems Too Good to Be True… It probably is. Be suspicious of online offers that appear too good to be true. These often lead to phishing scams or malware downloads.
- When in Doubt, Seek Help: If you’re ever unsure about the legitimacy of a website, email, or attachment, don’t be afraid to ask for advice. Consult with a tech-savvy friend, family member, or IT professional.
Final Thoughts
The internet has the potential to enrich our lives in countless ways. By adhering to these online safety rules and exercising caution and mindfulness, you’ll unlock a treasure chest of experiences while minimizing the risks.











Post Comment